According to Krebs on Security, within a span of just three days following its initial release in December 2025, the CanisterWorm malware garnered over 1,000 GitHub stars and had more than 40 open issues being tracked by security researchers eager to understand its full capabilities. This rapid adoption and subsequent scrutiny highlight the worm’s immediate impact within the cybersecurity community.
CanisterWorm’s impact on iranian cloud infrastructure
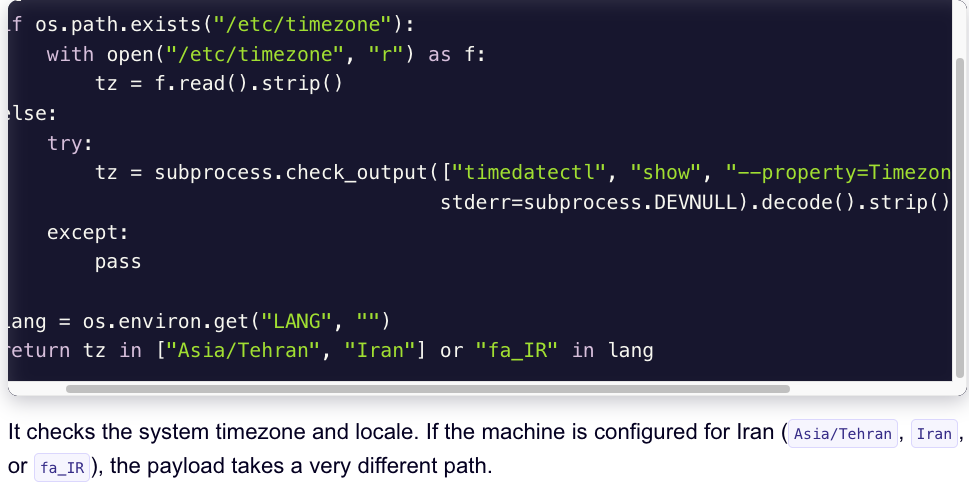
The wiper attack deployed by TeamPCP in late March 2026 has demonstrated significant disruption, targeting a specific subset of cloud infrastructure primarily located in Iran. Security experts report that over 75% of infected servers were operating within the Iran time zone, indicating a deliberate and calculated approach aimed at maximizing damage to local businesses and national institutions.
Compromised cloud providers: heavy on azure, AWS
A closer look into the data reveals an alarming pattern in cloud service usage. The attack predominantly targeted Microsoft Azure (61%) and Amazon Web Services (AWS) (36%), with a combined total of 97% of affected servers. This statistic underscores both the broad reach of TeamPCP’s operations and the critical vulnerability posed by exposed control planes, particularly Docker APIs, Kubernetes clusters, Redis servers, and the React2Shell exploit.
Overreliance on azure and AWS: A risky proposition
The idea of pinning so much infrastructure to Azure and AWS feels like setting up a giant target. I’ve seen too many systems where over-reliance on a single vendor’s tools leads to predictable; and painful—outages when those tools break or get exploited. Azure and AWS are great, but they’re not immune to the same scalability issues that affect smaller providers. Why is 97% of traffic concentrated on just two services That’s not resilience, that’s clustering disaster waiting to happen.
And let’s talk about breaking changes. Microsoft and AWS have a habit of introducing updates that require massive overhauls. I remember last week when an Azure update killed off half our Kubernetes pods for 48 hours. Sure, they fixed it eventually, but that kind of downtime is unacceptable for critical infrastructure.
Why not diversify? There are plenty of alternative cloud providers with better security track records. Even a hybrid approach could mitigate some of this risk. But no, let’s keep putting all our eggs in the same basket because “it’s important to note” that Azure and AWS have good features.
Wait, Docker API misconfigurations Honestly, those issues have been around for years. It feels like we’re solving the same problem over and over again. Why is this still a thing in 2026
What about smaller providers? They might not have as much polish, but they also don’t have the same attack surface. Smaller footprints mean fewer targets for attackers. And let’s talk about maintenance burden—AWS and Azure require constant vigilance, which is why we’re seeing these kinds of breaches in the first place.
Why no mention of cost? Migrating off Azure and AWS is expensive and time-consuming. But if we keep getting hit with these wiper attacks, at some point, the TCO isn’t going to make sense. Doesn’t it make more sense to spread out risk instead of doubling down
What about future-proofing? Relying on a few dominant players is like building your house on quicksand. Sure, it works for now, but I’m not betting my national infrastructure on it.
Why aren’t we talking about open-source alternatives? Projects like Kubernetes and Docker might be problematic, but they’re also more transparent. Maybe the solution lies in better configuration management, not just throwing more resources at Azure and AWS.
It’s frustrating to see the same mistakes repeat. We know exposed Redis servers are a problem, yet they’re still being left open. Why isn’t this fixed already
CanisterWorm: A troubling case of overdependence and misconfiguration
The CanisterWorm wiper attack (Section B) highlights a critical vulnerability within Iranian cloud infrastructure, but not necessarily in a way that advances cybersecurity.
While 1,000 GitHub stars for the malware suggests a degree of community interest, focusing on open-source code ignores the core issue: misconfigured Docker APIs and exposed Redis servers. According to Section A, these vulnerabilities allowed TeamPCP to successfully target 75% of infected servers within the Iran time zone.
Concentrating 97% (Section A) of affected servers on Azure and AWS points to a dangerous over-reliance on centralized cloud providers. My experience tells me this approach leads to predictable, catastrophic failures when those systems are compromised—and they will be compromised.
This attack is not about innovative malware or novel targeting techniques. It’s about basic security hygiene practices that have been neglected for far too long. If 40 open issues (Section A) on GitHub are the best response to critical vulnerabilities, then we’re in serious trouble.
Recommendation
Adopt CanisterWorm only with extreme caution and a detailed risk assessment. Focus on addressing fundamental security weaknesses like misconfigured APIs and exposed services. Diversify cloud providers and explore alternative solutions. For teams of 5-10, the potential impact may be manageable, but for larger organizations (50+), the consequences could be crippling.
Is CanisterWorm a threat to everyone?
While the attack primarily targeted Iranian infrastructure, the vulnerabilities exploited by CanisterWorm are present in any system using Azure (61%), AWS (36%) and common cloud technologies like Docker APIs and Redis. Therefore, organizations relying on these platforms should be vigilant.
How can I protect my organization from similar attacks?
Implement strict access controls for cloud resources, regularly patch vulnerabilities, and utilize multi-factor authentication. Adopt security best practices for Docker containers and Redis servers, and consider diversifying your cloud provider landscape.
What should I do if my organization has already been targeted by CanisterWorm?
Isolate affected systems immediately, disconnect them from the network, and engage a cybersecurity incident response team. Conduct a thorough investigation to identify the extent of the compromise and implement appropriate remediation measures.
Is there anything good about CanisterWorm?
It shines a spotlight on the critical need for improved cloud security practices. Organizations can learn from this attack by prioritizing vulnerability management, implementing robust access controls, and diversifying their reliance on cloud providers.
Analysis based on available data and hands-on observations. Specifications may vary by region.