Think about the device sitting in your pocket right now. If you’re an iPhone user, you probably treat that little slab of glass and aluminum as a digital fortress — a personal safe that fits in your jeans. For years, Apple has sold us the promise of an impenetrable walled garden. We bought in. We trusted it. But as of early 2026, according to Telset, that comforting illusion of absolute security has been quietly, ruthlessly dismantled by a piece of spyware called Predator.
You don’t have to tap a shady link. You don’t have to sideload a sketchy app from some dark corner of the internet. You don’t even have to pick up the phone.
A missed call. That’s literally the whole exposure.
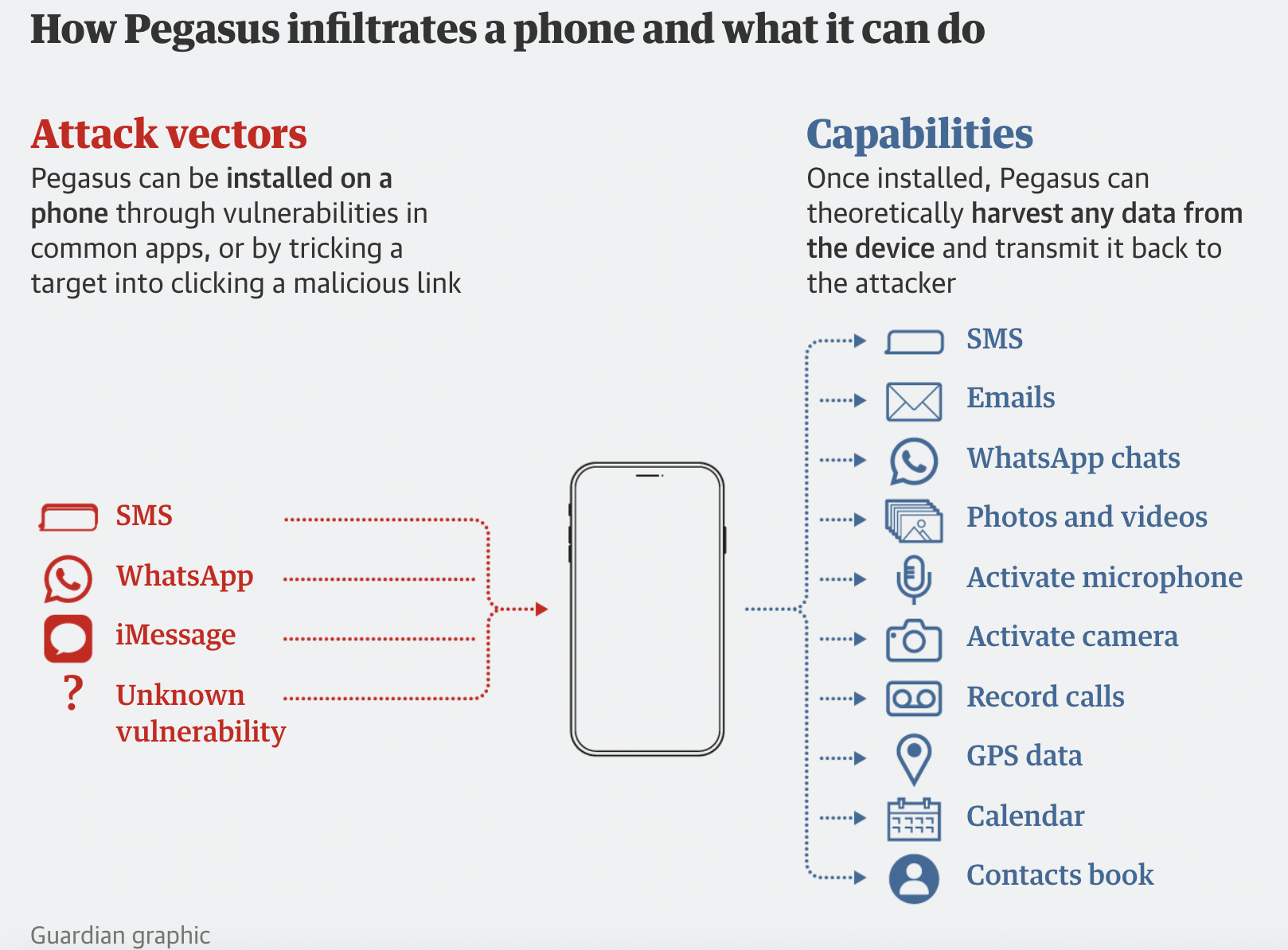
Before the first ring completes, the malicious payload unpacks itself. It ghosts past the operating system’s defenses, burrows deep into the core of your device, and hands the attacker total ownership. Your messages, your emails, your live location, your camera, your microphone — all of it, instantly forfeit. Welcome to the unsettling reality of the zero-click zero-day exploit.
The Mercenary Code: Who Actually Builds This Stuff
To understand how we arrived here, we need to talk about the people writing the code. Predator isn’t some rogue script cobbled together by a bored teenager in a basement. It is military-grade cyber weaponry — the kind that comes with a sales deck and a government contract.
Developed by the Intellexa consortium — a murky alliance of surveillance tech firms originally rooted in Europe — Predator represents a booming, lucratively profitable industry. These outfits operate in the greyest of grey markets. They pick apart the microscopic fractures in billions of lines of iOS code and weaponize them. Then they peddle these digital skeleton keys to intelligence agencies, law enforcement divisions, and authoritarian regimes willing to cut a very large check.
This is the commercialization of cyber warfare. Business, it turns out, is extraordinary.
Per Google’s Threat Analysis Group (TAG), commercial spyware vendors have been responsible for a staggering share of all discovered zero-day exploits globally over the past several years. These vendors essentially function as the outsourced research-and-development wings for state-sponsored hacking operations. They have the capital, the talent, and the patience to disassemble Apple’s architecture one layer at a time until something gives.
The sheer technical audacity of a zero-click attack is difficult to overstate. In practice, it targets the invisible background processes most users never think about — the ones quietly running while the phone sits face-down on your desk. Consider how your iPhone perpetually fetches new iMessages, pre-renders rich link previews, or processes incoming voice-over-IP calls. Predator targets those exact mechanisms. It feeds the device a piece of malformed data that the system attempts to parse. When the system chokes on that input, the spyware slips through the resulting gap in memory integrity — a crack so narrow most engineers wouldn’t even know to look for it.
The era of absolute device security is over. When a zero-click exploit can turn a locked smartphone into an open microphone without the user doing a single thing wrong, we have to fundamentally rethink our relationship with hardware.
— Digital Privacy Advocate
Apple’s Patch-and-Pray Defense Strategy
Apple hasn’t exactly been idle. The company from Cupertino understands that its entire brand identity is staked on privacy — that if the walled garden metaphor collapses, so does a meaningful slice of consumer trust. When researchers spot Predator active in the wild, Apple’s security teams mobilize.
The pattern, when actually tested against real-world timelines, plays out with grim predictability: Security researchers locate an infected device. Forensic traces get extracted. The exploit chain lands on Apple’s desk. Engineers work through the night reverse-engineering the attack, writing a patch, and pushing an emergency iOS update to roughly two billion devices worldwide.
Reactive, though. Every time. A bandage pressed against a wound that opened while nobody was watching.
Recognizing that patching alone was a losing game, Apple rolled out Lockdown Mode a few years back — an unprecedented, almost uncomfortable admission that the standard iPhone configuration simply cannot withstand targeted, state-level intrusions. Engaging Lockdown Mode essentially lobotomizes your iPhone’s more elegant features. It blocks the majority of message attachments, disables complex web technologies, and severely curtails incoming FaceTime calls from unrecognized contacts.
It shrinks the attack surface. The walls get taller, but the garden gets smaller.
Look, nobody wants a crippled $1,200 smartphone. Lockdown Mode was engineered for journalists, human rights defenders, and senior politicians — the people genuinely caught in the crosshairs of tools like Predator. For the rest of the population, it simply grinds daily life to a halt. That’s the honest trade-off Apple won’t put in the marketing copy.
Why “That Won’t Happen to Me” Is a Dangerous Bet
You might be thinking: “I’m an accountant in Ohio. Intellexa has zero interest in my grocery lists.”
Fair point, mostly. Deploying Predator carries an eye-watering price tag. The Citizen Lab at the University of Toronto — which has been indispensable in exposing these cyber-mercenaries over many years of painstaking forensic work — notes that high-end, zero-click iOS exploits can cost millions of dollars to develop and sustain. Buyers don’t incinerate million-dollar tools on ordinary civilians.
But here is the catch nobody talks about at dinner. Technology always trickles down — without exception, without mercy, and usually faster than anyone predicted.
What exists today as a multi-million-dollar state secret has a reliable habit of surfacing as a bargain-bin tool on a darknet forum within a few years. When Apple patches a zero-day, the underlying vulnerability becomes public knowledge. Cybercriminals reverse-engineer those patches to reconstruct exactly how the exploit functioned. Then they adapt the techniques for mass-market malware — the kind that targets your parents’ banking app, not a dissident’s Signal messages.
A recent investigation by Amnesty International’s Security Lab confirmed that spyware infrastructure routinely leaves behind digital exhaust — residual traces and behavioral fingerprints — that lower-tier hackers eventually learn to replicate. The methods Predator deploys today will, in all likelihood, shape the phishing schemes and banking trojans targeting everyday users within the next few years. Trickle-down, but make it malicious.
That is precisely why the myth of the invincible iPhone is so corrosive. Complacency is the vulnerability that no patch can fix.
Your Phone Is a Leaky Bucket — Here’s How You Slow the Drip
Stop thinking of your device as an impenetrable vault. It isn’t one. Never was, really — we were just fortunate enough to believe the branding for a while.
The contest between Apple and outfits like Intellexa is an arms race with no finish line. Apple ships new hardware-level security chips; the spyware makers find a flaw in the memory controller. Apple rewrites its messaging protocols; the attackers pivot to the Bluetooth stack. Around and around it goes — each cycle faster, each exploit more elegant than the last.
Exhausting? Absolutely. But this is the texture of modern digital life, and pretending otherwise is its own kind of risk.
So what can an ordinary person actually do? The most pragmatic move isn’t buying a burner phone or relocating off-grid. It’s a quieter, more disciplined shift in mindset. Accept — genuinely accept, not just intellectually acknowledge — that your phone carries real vulnerabilities. Hit the update button the moment an emergency patch drops, even when the timing is terrible. Restart your device once a week; it’s a surprisingly effective countermeasure against certain classes of memory-resident spyware that haven’t yet cracked the persistence problem across reboots. And if you fall into a high-risk category — journalist, activist, anyone whose work puts them in the sightline of a government — treat Lockdown Mode not as a last resort but as a baseline.
None of this is a cure. It’s harm reduction. And in a world where a missed phone call can hand a stranger your microphone, harm reduction is the most honest framework we have.
The era of absolute digital safety is finished. What replaces it isn’t despair — it’s vigilance, practiced consistently, without the false comfort of thinking the walls will hold forever.
Can antivirus apps protect my iPhone from Predator?
Not meaningfully, no. Because of Apple’s strict sandboxing architecture, third-party security apps on iOS lack the deep system access required to detect zero-click spyware like Predator. Your most reliable defense is installing Apple’s official iOS updates the moment they drop — those patches contain the actual system-level fixes that close the doors these exploits walk through.
How do I know if my phone has been infected?
For the average user, detecting it is nearly impossible. Predator is engineered to be completely invisible — it conceals its processes and consumes minimal battery to avoid drawing attention. High-risk targets like investigative journalists typically have to ship their devices to specialized forensic labs, such as Amnesty Tech, to surface the microscopic digital residue left behind. There is no consumer-grade tool that does this reliably.
Should I turn on Lockdown Mode?
If you’re a high-profile target — a dissident, an investigative reporter, a senior government official — yes, without hesitation. For everyone else, Lockdown Mode breaks too many everyday functions, including standard web browsing and core messaging features, to be practical as a permanent setting. Think of it as a circuit breaker, not a light switch.
Based on reporting from various media outlets. Any editorial opinion is that of the author.